
Back Mühafizə halqaları Azerbaijani Anells (seguretat informàtica) Catalan Privilegovaný režim Czech Privilegienstufe German Anillo (seguridad informática) Spanish حلقه حفاظتی Persian Anneau de protection French Ռինգ Armenian Domini gerarchici di protezione Italian リングプロテクション Japanese
This article includes a list of general references, but it lacks sufficient corresponding inline citations. (February 2015) |
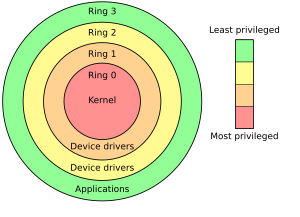
In computer science, hierarchical protection domains,[1][2] often called protection rings, are mechanisms to protect data and functionality from faults (by improving fault tolerance) and malicious behavior (by providing computer security).
Computer operating systems provide different levels of access to resources. A protection ring is one of two or more hierarchical levels or layers of privilege within the architecture of a computer system. This is generally hardware-enforced by some CPU architectures that provide different CPU modes at the hardware or microcode level. Rings are arranged in a hierarchy from most privileged (most trusted, usually numbered zero) to least privileged (least trusted, usually with the highest ring number). On most operating systems, Ring 0 is the level with the most privileges and interacts most directly with the physical hardware such as certain CPU functionality (e.g. the control registers) and I/O controllers. With the increasing prevalence of virtualization, many CPUs have added another level (conceptually ring -1) for the hypervisor.
Special mechanisms are provided to allow an outer ring to access an inner ring's resources in a predefined manner, as opposed to allowing arbitrary usage. Correctly gating access between rings can improve security by preventing programs from one ring or privilege level from misusing resources intended for programs in another. For example, spyware running as a user program in Ring 3 should be prevented from turning on a web camera without informing the user, since hardware access should be a Ring 1 function reserved for device drivers. Programs such as web browsers running in higher numbered rings must request access to the network, a resource restricted to a lower numbered ring.
- ^ Karger, Paul A.; Herbert, Andrew J. (1984). An Augmented Capability Architecture to Support Lattice Security and Traceability of Access. 1984 IEEE Symposium on Security and Privacy. p. 2. doi:10.1109/SP.1984.10001. ISBN 0-8186-0532-4. S2CID 14788823.
- ^ Binder, W. (2001). "Design and implementation of the J-SEAL2 mobile agent kernel". Proceedings 2001 Symposium on Applications and the Internet. pp. 35–42. doi:10.1109/SAINT.2001.905166. ISBN 0-7695-0942-8. S2CID 11066378.
© MMXXIII Rich X Search. We shall prevail. All rights reserved. Rich X Search